Original URL: http://www.theregister.co.uk/2008/08/22/accessing_restricted_sites/
That password-protected site of yours - it ain't
It's one of the simplest hacks we've seen in a long time, and the more elite computer users have known about it for a while, but it's still kinda cool and just a little bit unnerving: A hacker has revealed a way to use Google and other search engines to gain unauthorized access to password-protected content on a dizzying number of websites.
While plenty of webmasters require their visitors to register or pay a fee before viewing certain pages, they are typically more than eager for search engine bots to see the content for free. After all, the more search engines that catalog the info, the better the chances of luring new users.
But the technique, known as cloaking, has a gaping loophole: if Google and other search engines can see the content without entering a password, so can you. Want to read this forum (http://forums.inkdropstyles.com/index.php?showtopic=4227) from the InkDrop Styles website? You can, but first you'll have to enter a user name and password. Or you can simply type "cache:http://forums.inkdropstyles.com/index.php?showtopic=4227" into Google. It leads you to this cache (http://209.85.141.104/search?hl=en&q=cache%3Ahttp%3A%2F%2Fforums.inkdropstyles.com%2Findex.php%3Fshowtopic%3D4227&btnG=Google+Search&aq=f), which shows you the entire thread.
The technique yields plenty of other restricted forums, including those here (http://209.85.141.104/search?hl=en&q=cache%3Ahttp%3A%2F%2Fpznetworks.com%2Findex.php%3Fshowtopic%3D3355%26view%3Dgetlastpost&btnG=Google+Search&aq=f), here (http://209.85.141.104/search?hl=en&q=cache%3Ahttp%3A%2F%2Fwww.chillcorner.com%2Findex.php%3Fshowtopic%3D1156&btnG=Google+Search&aq=f) and here (http://supex0.co.uk/xforums/index.php?showtopic=16).
Those in the know have been using the trick for years, but a hacker who goes by the handle Oxy recently made this post (http://hackforums.net/showthread.php?tid=25040) that shares the technique with the world at large. It reminds us of a similar approach for accessing restricted sites that involves changing a browser's user agent to one used by search engine bots.
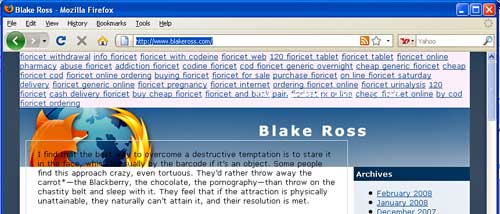
The hack is one example of the security problems that result from the practice of cloaking. Robert Hansen, the web security guru and CEO of secTheory (http://sectheory.com/) recently alerted us to the compromised blog (http://www.blakeross.com/) of Blake Ross, the co-founder of the Mozilla Firefox project who recently went to work for Facebook. For more than a month, unknown miscreants have been using his site to host links to sites pushing diet pills and other kinds of drugs.
Thanks the some javascript magic, users who visit the site never see evidence of the compromise, i.e. the links are cloaked. But the image below shows what happens when javascript is disabled.
We've contacted Blake about his website, but haven't yet received a response. Cleaning up the site ought to be as easy as updating his badly out-of-date version of WordPress. Addressing the shadowy world of cloaking will take a bit more work. ®
Related stories
Cloud computing lets Feds read your email (20 August 2008)
http://www.theregister.co.uk/2008/08/20/cloud_computing_privacy/
Security researchers' accounts ransacked in embarrasing hacklash (13 August 2008)
http://www.theregister.co.uk/2008/08/13/security_researchers_targeted/
Rogue reporters kicked out of conference for network snooping (8 August 2008)
http://www.theregister.co.uk/2008/08/08/black_hat_snoops/
Open Wi-Fi network wraps Mumbai man in bomb blast probe (1 August 2008)
http://www.theregister.co.uk/2008/08/01/terrorist_email/
Oops - SF prosecutors put city passwords on public record (28 July 2008)
http://www.theregister.co.uk/2008/07/28/sf_rogue_sysadmin_password_mess/
© Copyright 2008



